Blue Team Labs Online - First Day

Today marks your first day on the job as a Malware Analyst. Your boss sends an unknown malicious sample over Slack to you; to put your skills to the test. He wants to see if you have the ability to research, report and fully analyse this sample without any mistakes.
Reverse Engineering
Tags: VirusTotal PEstudio OSINT Procmon IDA T1041 T1055.001
Scenario Today marks your first day on the job as a Malware Analyst. Your boss sends an unknown malicious sample over Slack to you; to put your skills to the test. He wants to see if you have the ability to research, report and fully analyse this sample without any mistakes. He concludes with a “Have fun! Don’t forget to take notes along the way”. Time to show him what you’ve learned over the past few months.
The sandbox machine you're using doesn't have an internet connection. To access VirusTotal and other online resources for research purposes, you should use your host machine and not the lab.
Investigation Submission
Q1) Can you identify the malware family of the provided sample? Research is key! (Format: Family Name)
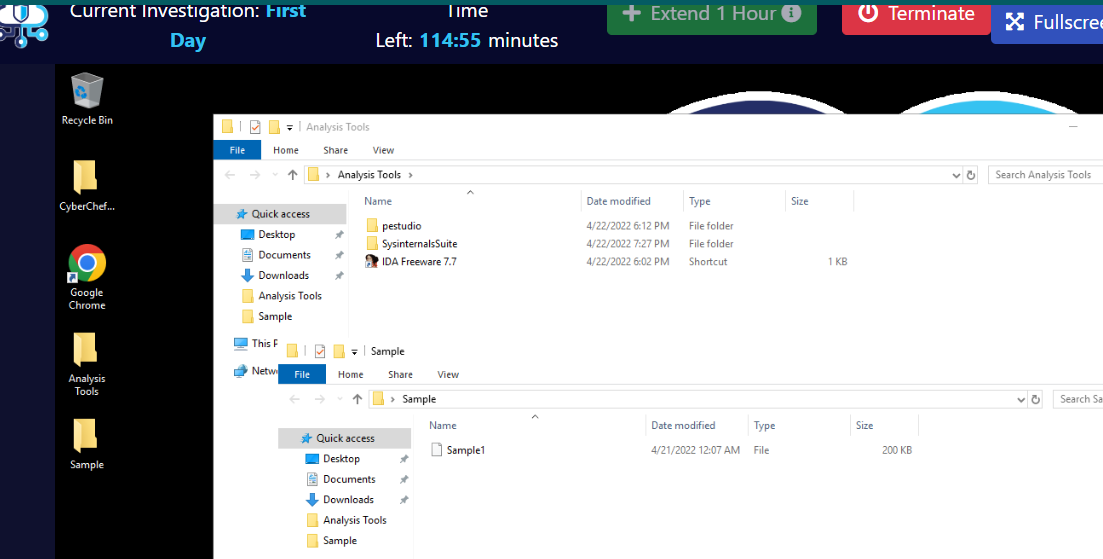
We have pestudio, IDE Freeware and SysinternalsSuite to analyze malware sample so lets start with calculate filehash using pestudio and search it online.
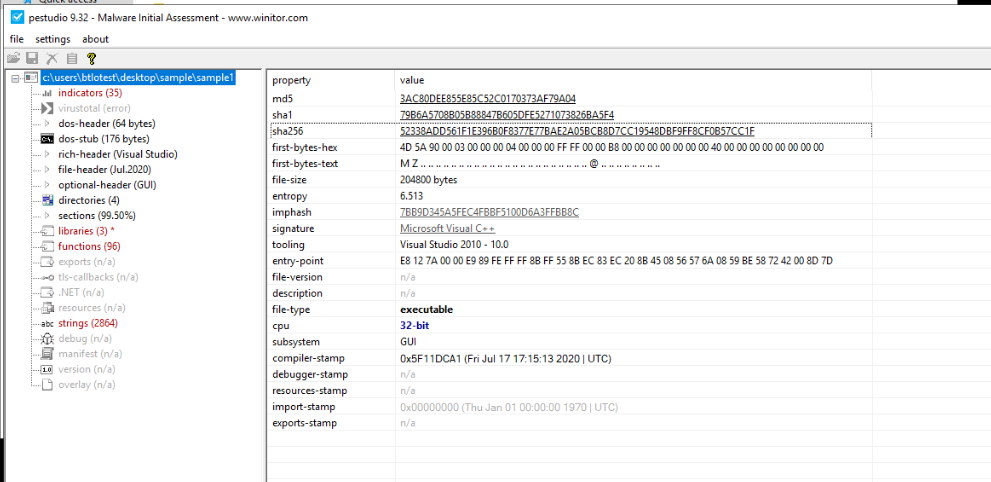
Then we can see beside of this hash, there are a lot of indicators telling us this file is not a simple file but a malware.
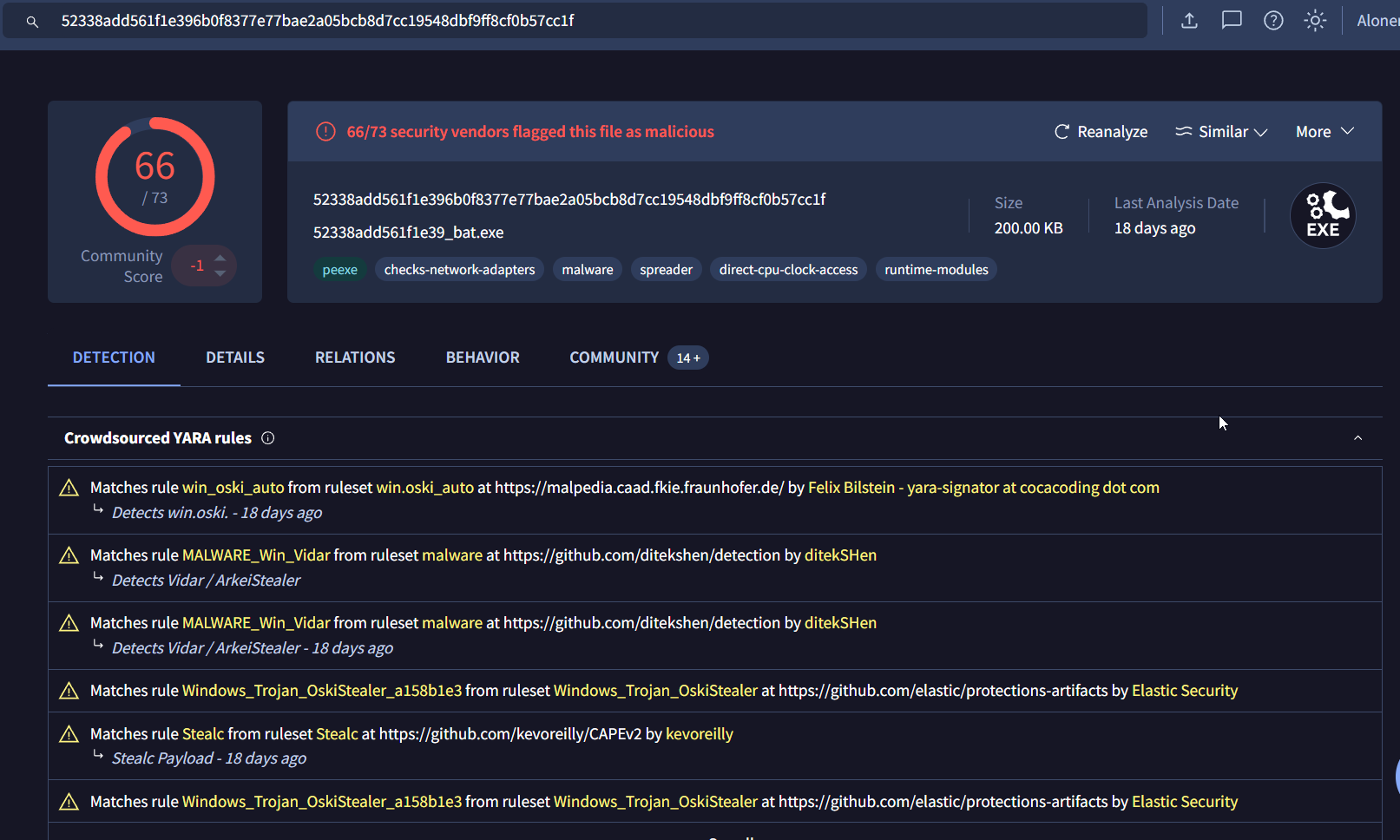
Search its hash on VirusTotal then we can see that it matched Stealc and Oski YARA rule so we have 2 choices here.
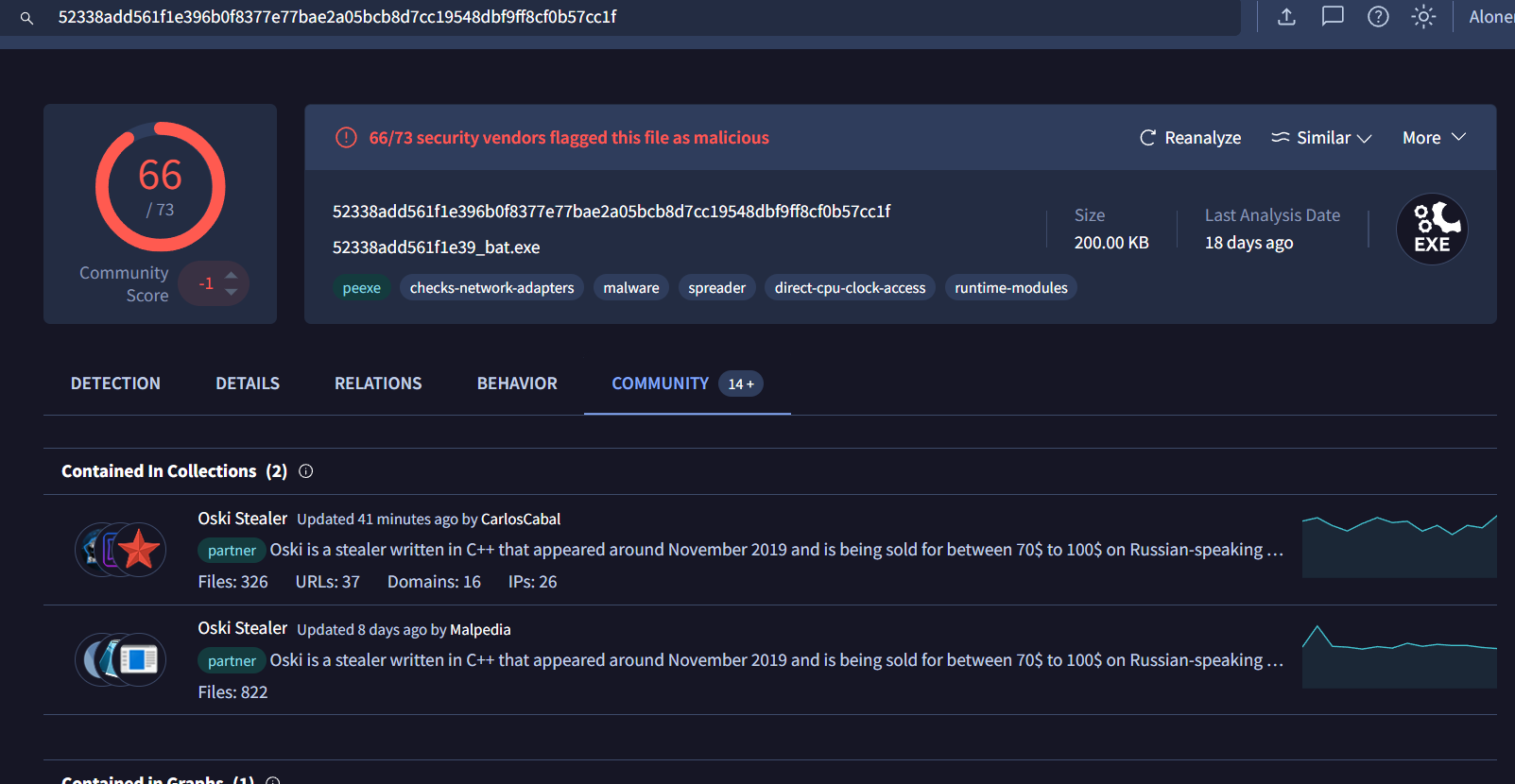
We can confirm it via Community tab that contained this file in Oski Stealer collection so this is Oski malware.
Answer
oskiQ2) This malware family is known to reach out to its C2 for files. Locate the C2 and find which country it is based in (Format: IP, country)
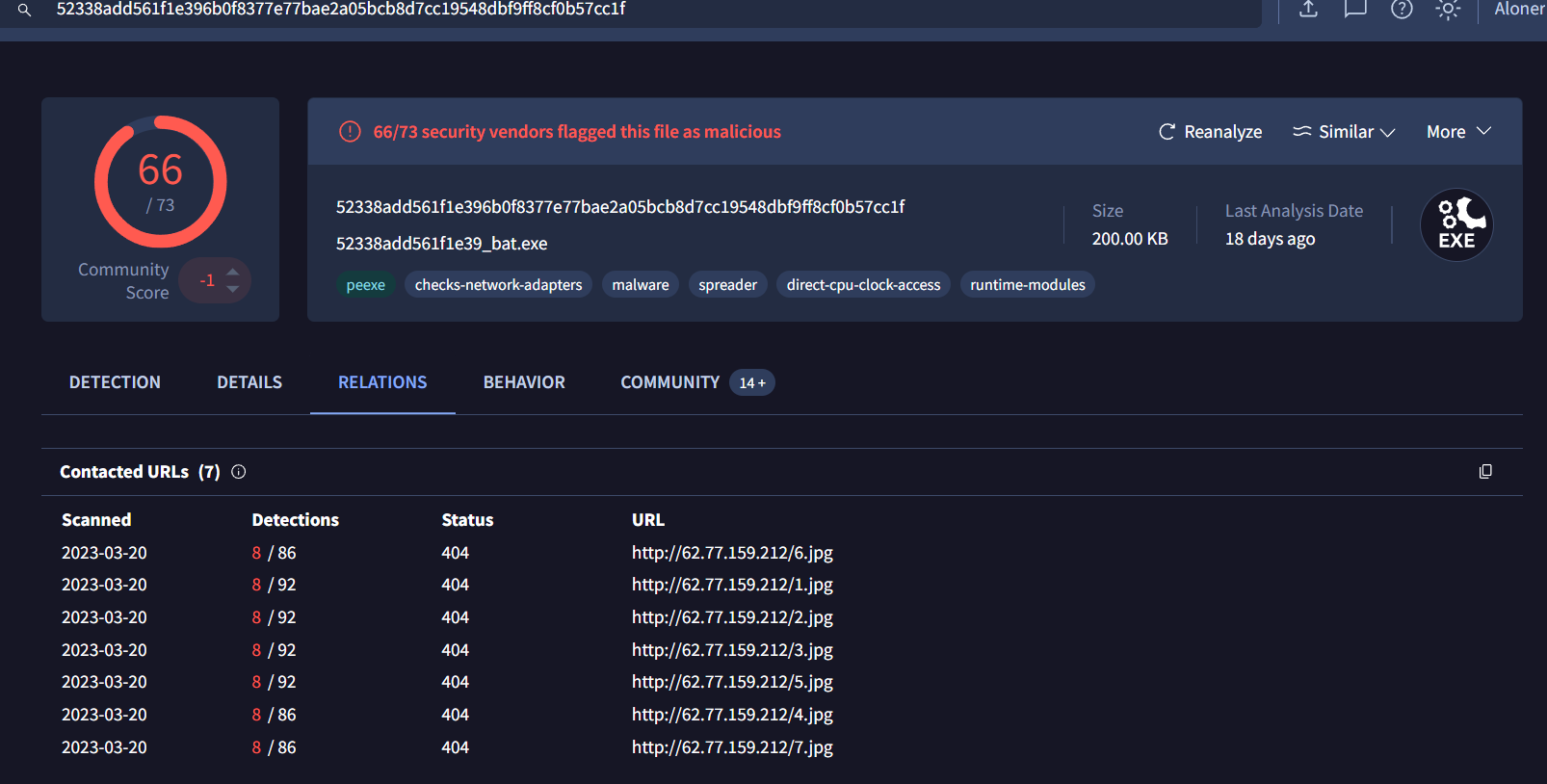
Go to Relation tab then we can see that this file will download 7 files from this IP address.
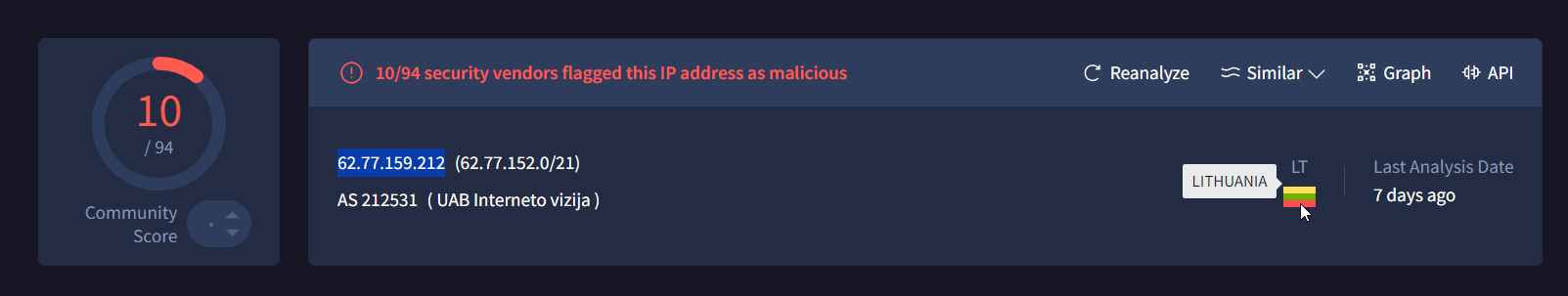
Then after followed this IP address on VirusTotal, we can see that its associated to Lithuania.
Answer
62.77.159.212, LithuaniaQ3) Commonly, this type of malware is known to download 7 additional files to aid in data exfiltration. List the files it downloads in alphabetical order (A-Z). (Hint: OSINT! Maybe someone else has researched this malware family before...) (Format: FileA.ext, FileB.ext, FileC.ext, ...)
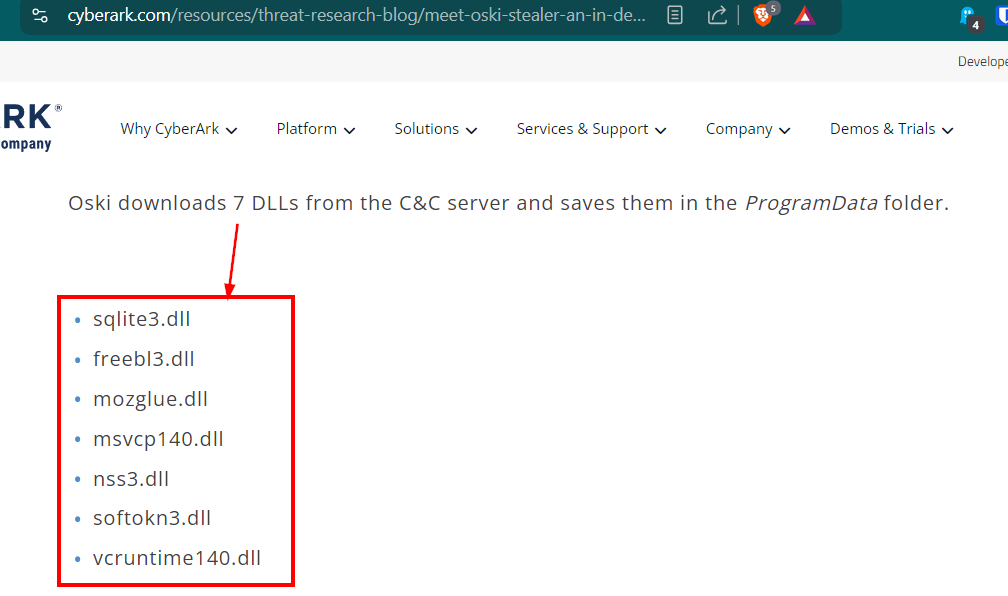
We can dig into each file on VirusTotal but OSINT is the most effective way to get an answer of this question, CyberAsk already published a blog about this malware and its capabilities which we can see that those 7 files we saw from VirusTotal are actually these 7 dll files
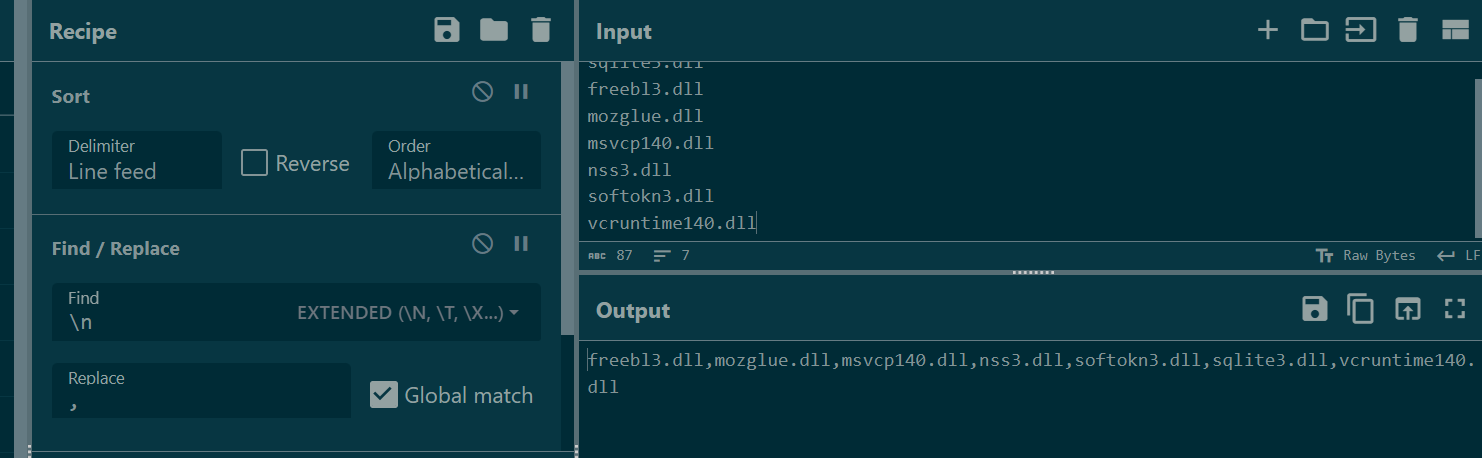
Copy them and let CyberChef or ChatGPT sort it to submit the correct answer.
Answer
freebl3.dll,mozglue.dll,msvcp140.dll,nss3.dll,softokn3.dll,sqlite3.dll,vcruntime140.dllQ4) Can you find the entry point of the malware? (Format: 0xXXXXXXXX)
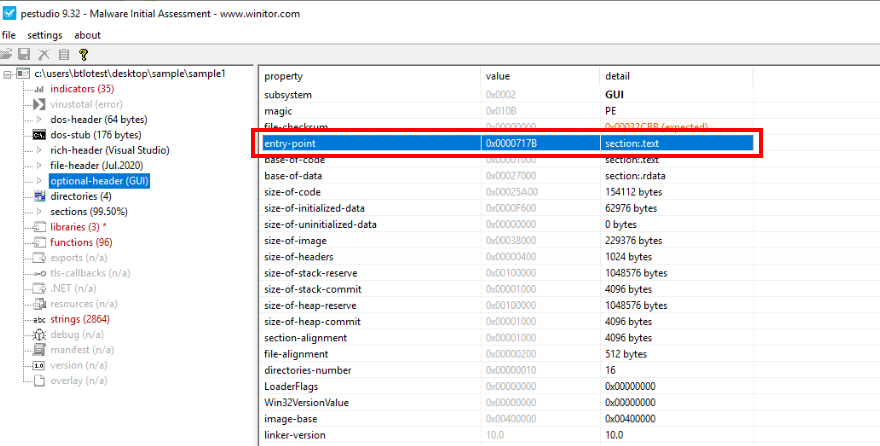
Back to pestudio then go to optional header which we can see entry-point address of the malware right here.
Answer
0x0000717BQ5) Exfiltration happens quick and you can miss it if you blink. Where is the folder located for data exfiltration? (Format: X:...)
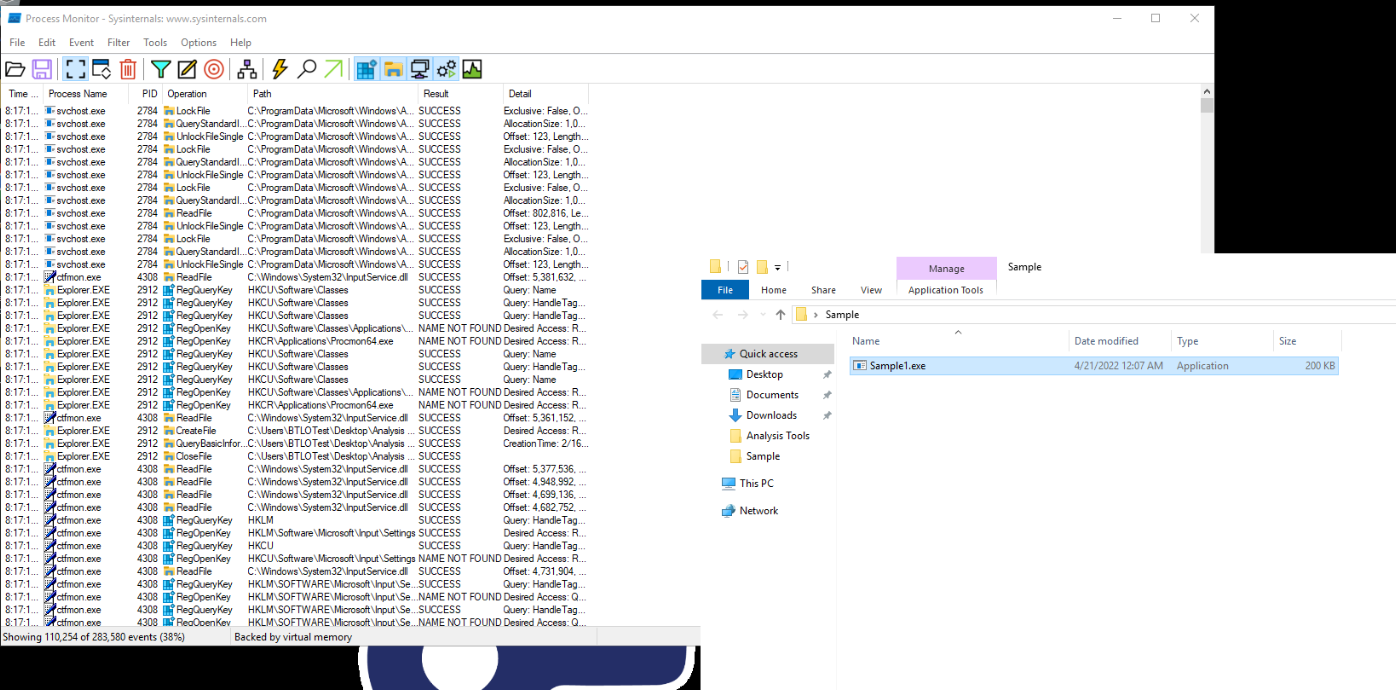
Its time for procmon! lets open procmon and execute the malware.
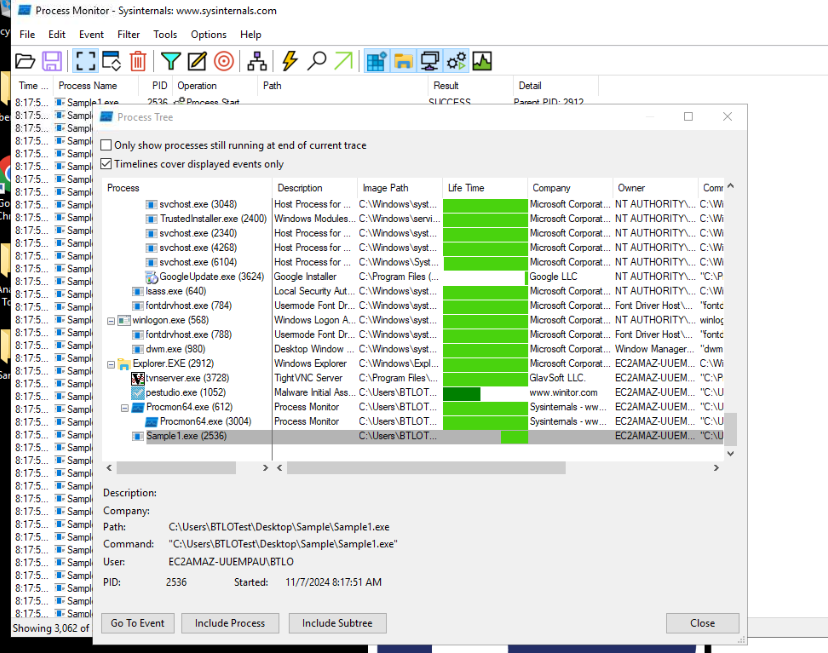
To make our life easier, go to "Tools" -> "Process Tree" to open process tree windows then we can add this malware process to our included list.
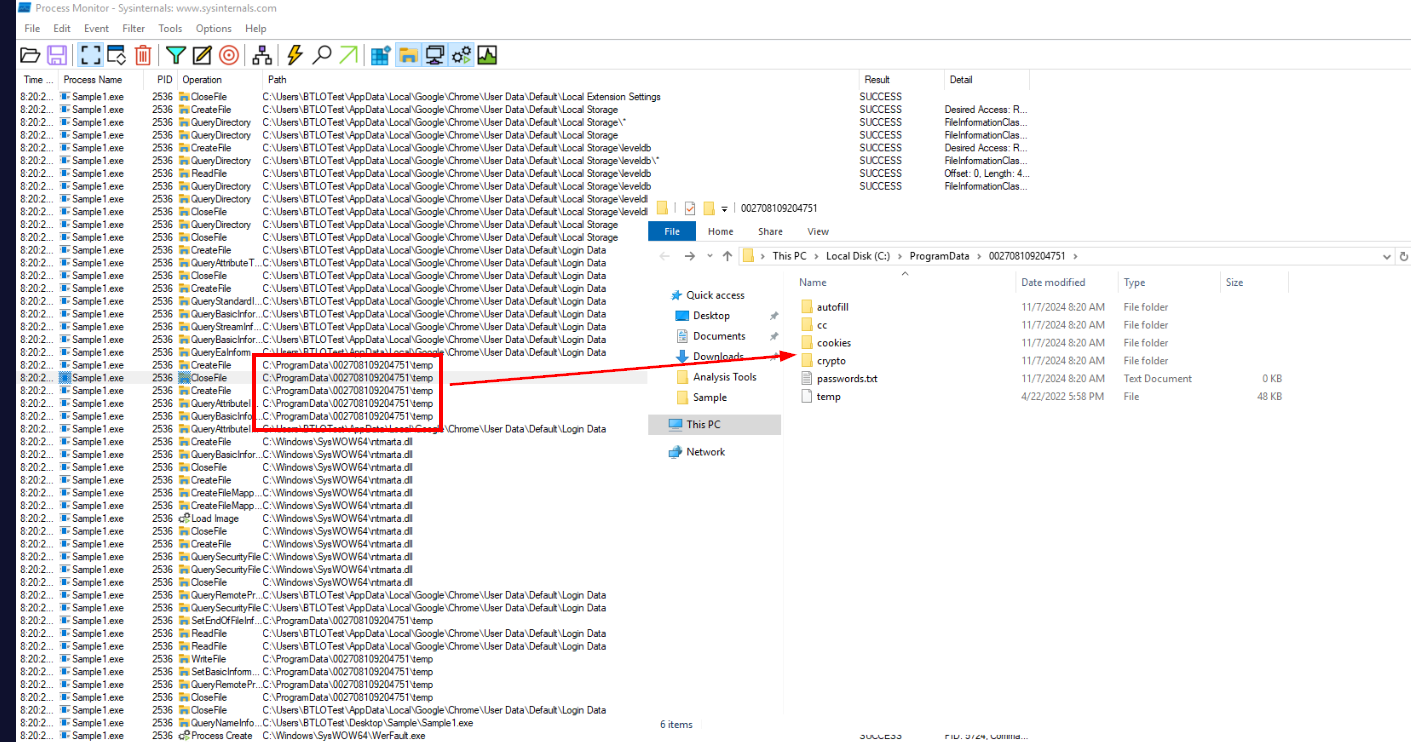
Then we can see that there is a folder under ProgramData that store files collected by a malware.
Answer
C:\ProgramDataQ6) Perform some research to identify the type of cipher used to obfuscate the strings and then locate its cipher key (Format: Cipher-type, numeric_key)
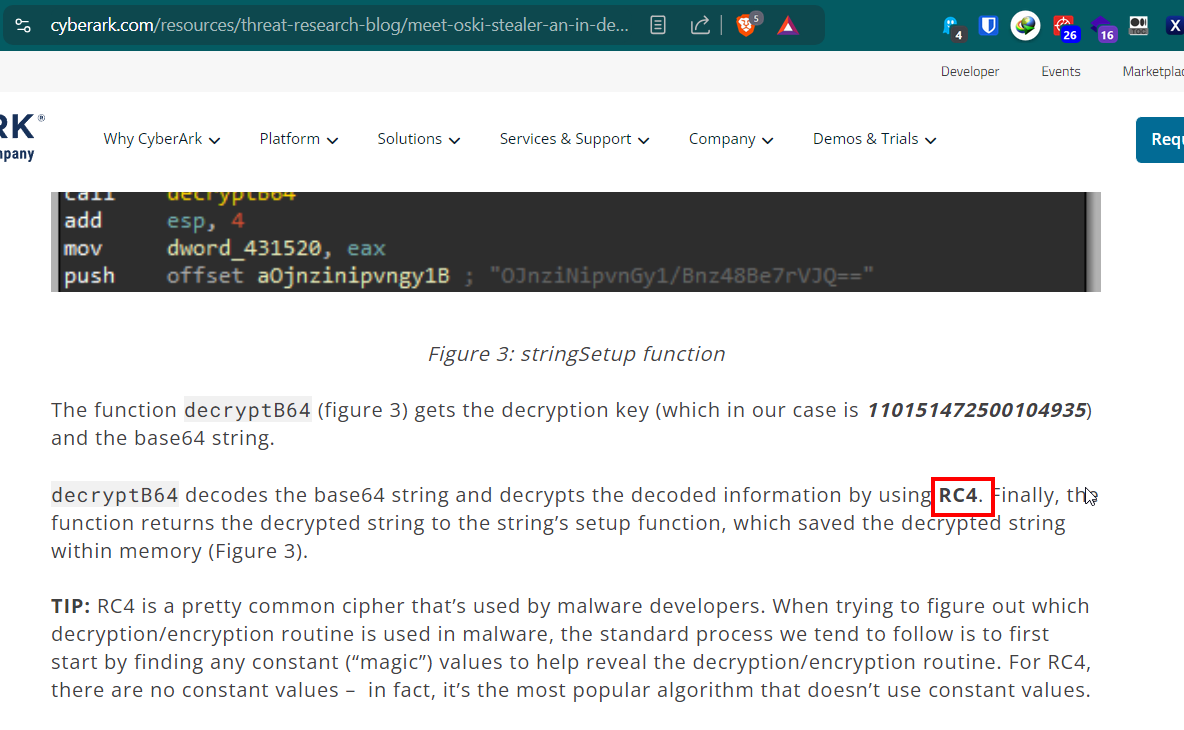
From CyberAsk blog, we know that this malware use RC4 to obfuscate the string so lets load this malware on IDA and find a key and try to find a function that resemble stringsSetup function.
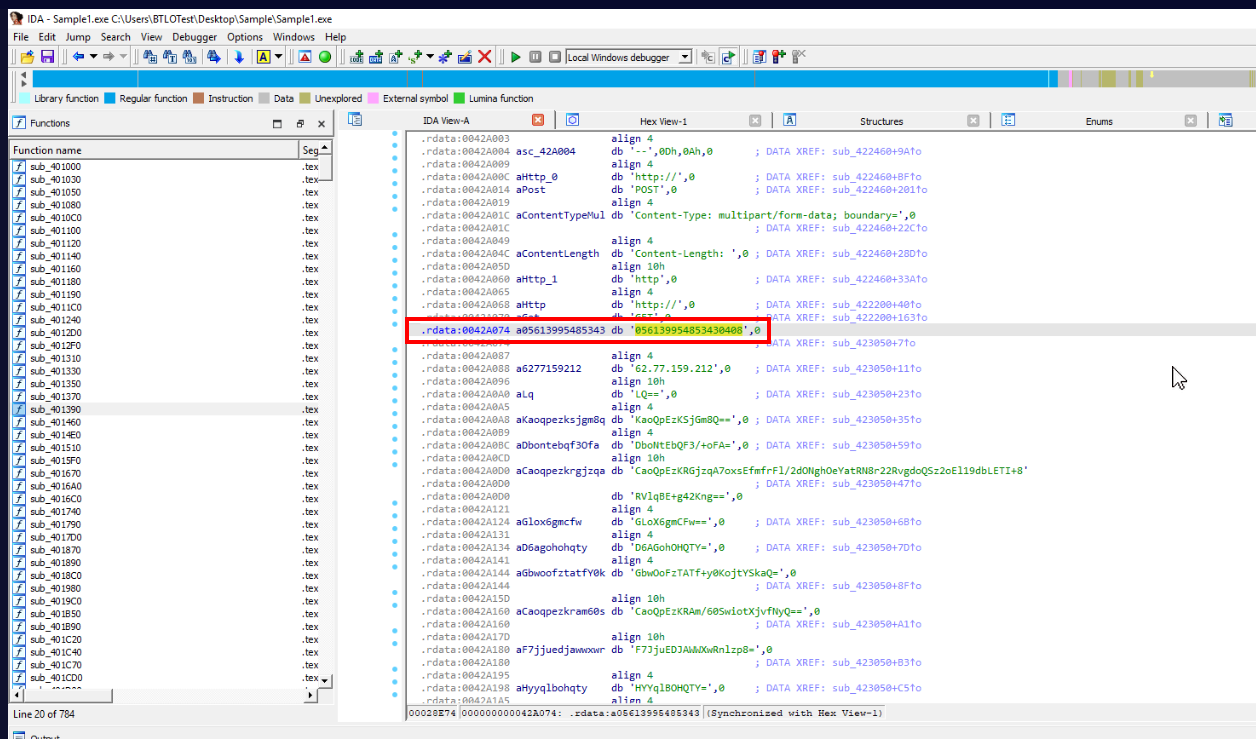
First I went to .rdata section of this malware that hold read-only data which I found this weird numerical number resemble a key format.
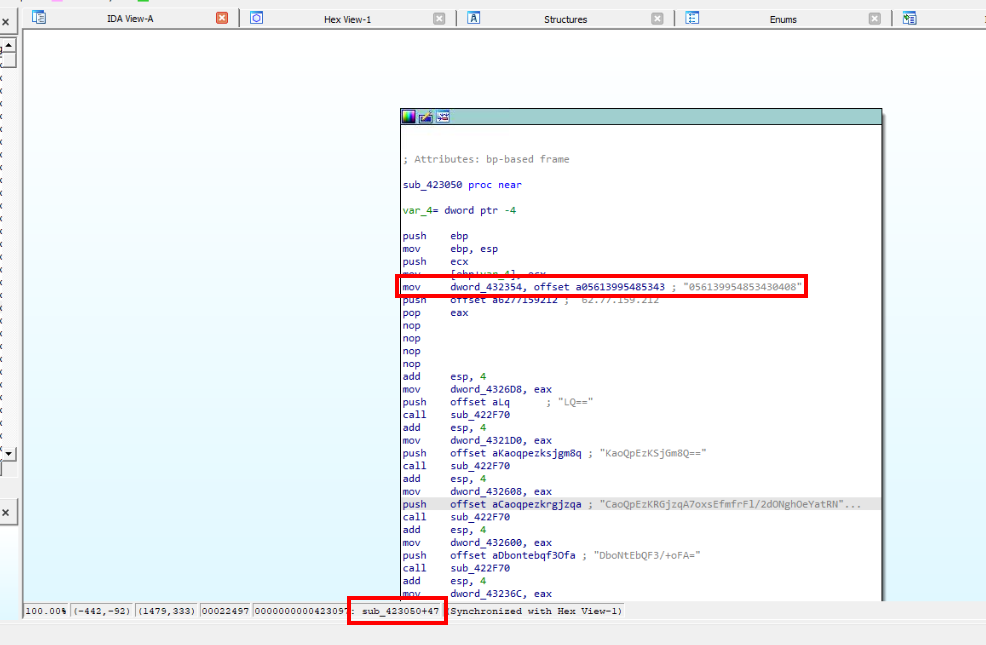
I followed it and sure enough, this is the key use for decryption!
Answer
RC4, 056139954853430408Q7) A configuration file is used to decide what needs to be exfiltrated. Find the name of this config and it’s filetype (Format: filename.ext)
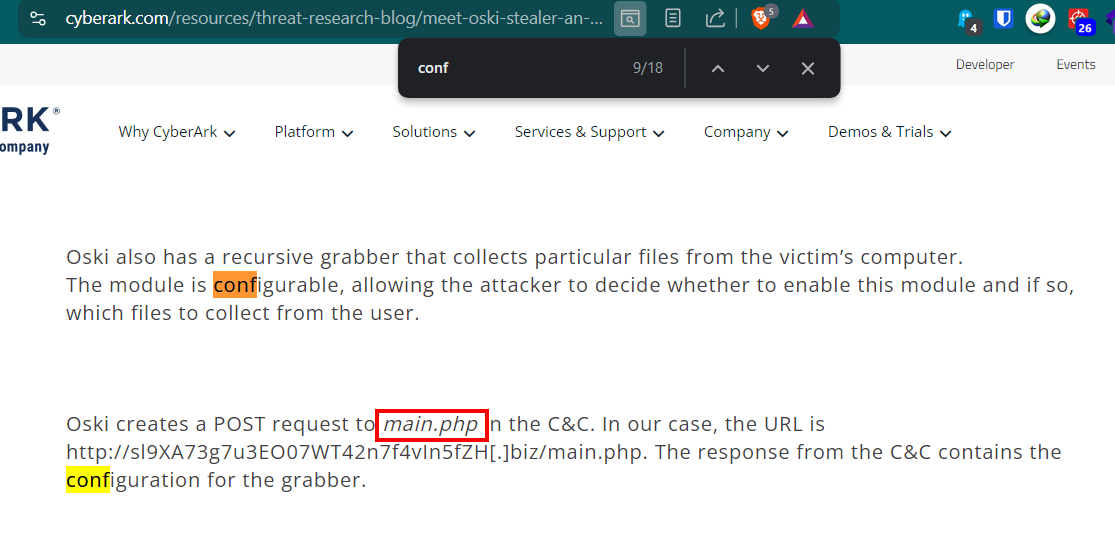
We can get the answer of this question by reading CyberArk blog right here.
Answer
main.php https://blueteamlabs.online/achievement/share/52929/101
https://blueteamlabs.online/achievement/share/52929/101